CYBERSECURITY RESEARCHER
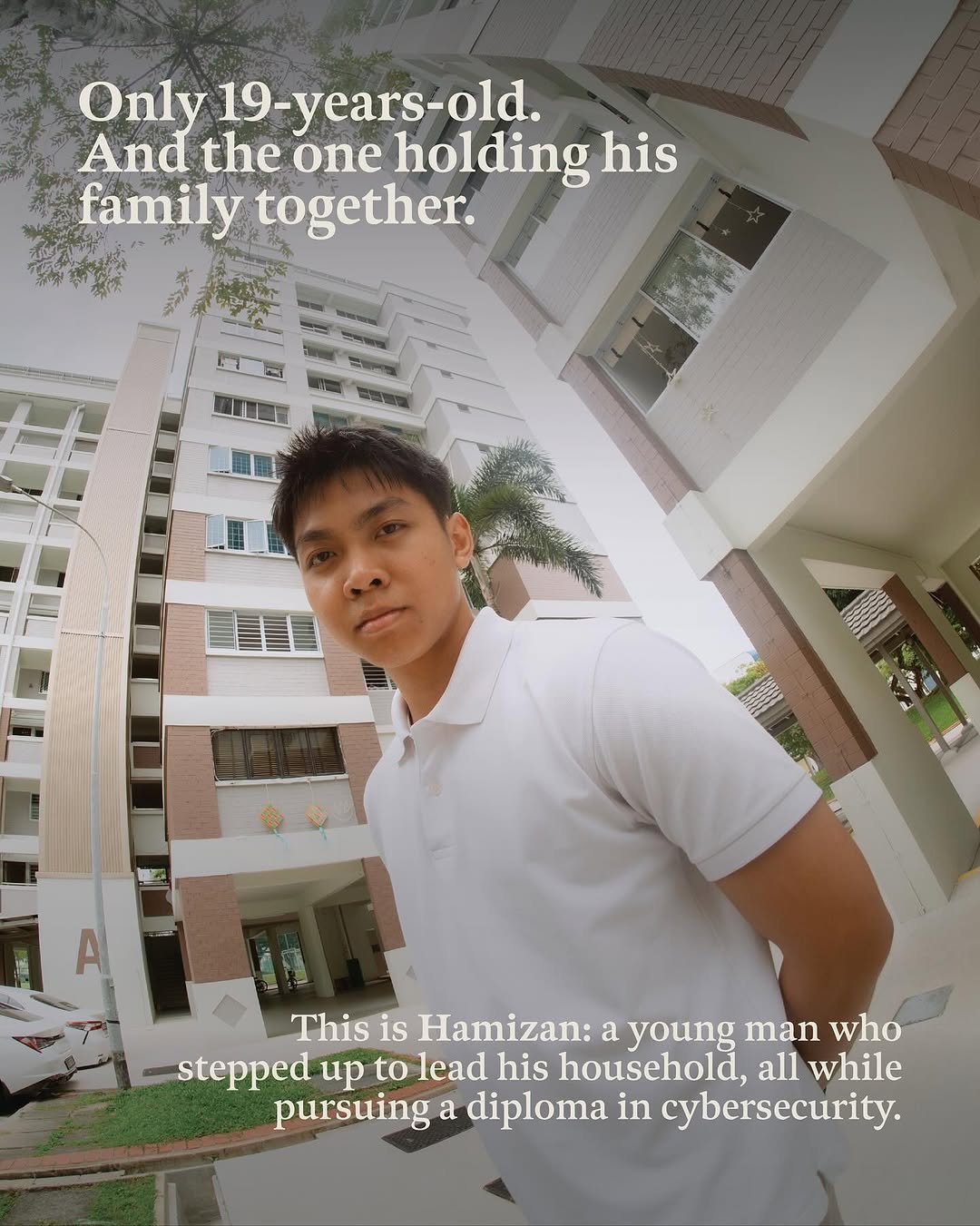
Hamizan Azman
Security researcher at Singapore Management University working on LLM security. Two CVEs rewarded so far. Leading Singapore's first polytechnic cybersecurity clinic and writing my first paper on LLMs with Prof Xie Xiaofei.






01 // ABOUT
I'm a 20-year-old cybersecurity researcher in Singapore, graduating from Cybersecurity and Digital Forensics at Temasek Polytechnic.
I research LLM security under Prof Xie Xiaofei at Singapore Management University, through the NTU CRPO Cyber Translation Programme. My work contributes to open source AI by analysing threats at the dependency level, building reproducible vulnerability environments, and threat modelling prompt injection paths through MCP servers.
I led the founding team of the TP Cybersecurity Clinic as its first Lead Student Ambassador, where we helped 38 small businesses across Singapore strengthen their security posture. The clinic is backed by The Asia Foundation and Google.org.
I also hunt vulnerabilities in open source authentication and protocol code. Two CVEs rewarded so far. The first, CVE-2026-27855 in Dovecot, scored a Medium 6.8. The second, reported via HackerOne, was accepted at 6.9. More disclosures are in progress with a collaborator.
I want to make the digital world safer for people who need it most.
QUICK FACTS
02 // EXPERIENCE
LLM Security Research Intern
Singapore Management University
NTU CRPO Cyber Translation Internship Programme
Research intern under Prof Xie Xiaofei. Working across LLM application security, supply chain analysis, and AI agent security at the open source ecosystem layer.
- Engineering features into an automated pentest platform of 26 microservices that orchestrate exploit generation, CVE search, and DOCX report generation behind a single entry port
- Reproduced 231 vulnerability PoCs as runnable shooting ranges, turning a static dataset into an executable corpus other researchers can clone and verify
- Containerised 79 open source LLM applications as reproducible Docker images and published 83 pinned images for the lab and outside researchers to consume
- Leading own research thread on automated detection of specification violations in LLM frameworks, working toward a first paper
- Drove a dependency pinning policy that makes unpatched windows visible across every deployed application
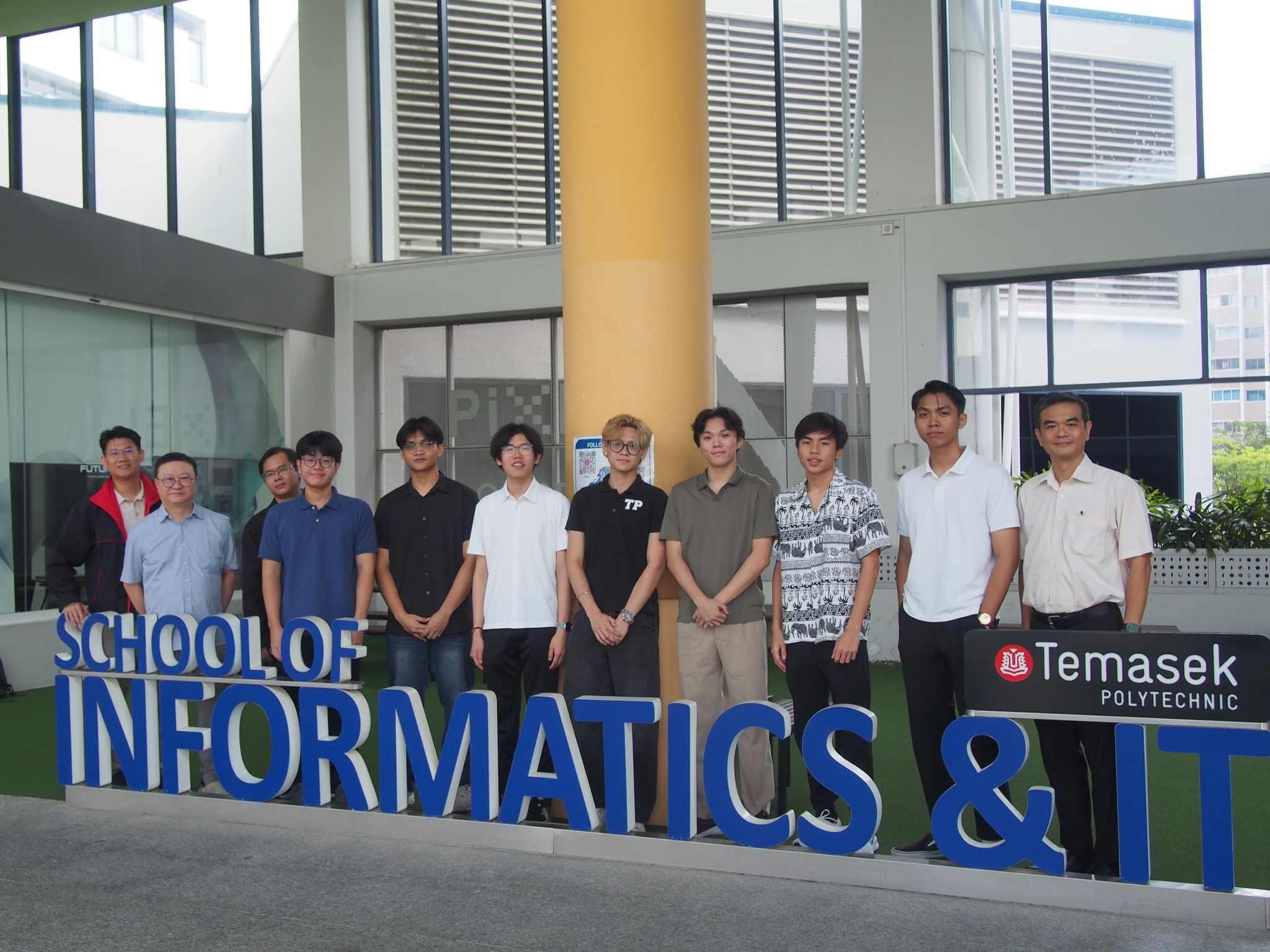
Lead Student Ambassador
TP Cybersecurity Clinic
Backed by The Asia Foundation & Google.org
Led the founding team as its first Lead Student Ambassador. Ran Singapore's first polytechnic based cybersecurity clinic serving micro, small, and medium enterprises across the nation.
- Personally conducted 12 on site cybersecurity programmes, the most of any ambassador
- Recruited, trained, and mentored 40 ambassadors
- Clinic supported 38 MSMEs across Singapore, with 3 companies returning for up to 4 engagements
- Instrumental in collaboration with NTU CRPO and clinic's entry into the CyberSG Consortium
- 2 companies offered internships on the spot during engagements
Malware Analyst Intern
TP Malware Analysis Centre
Contributed to deepfake detection research and represented Temasek Polytechnic at national events. Conducted independent malware reverse engineering.
- Presented DeepVysion+ (Best Major Project 2024) at GovWare 2025 to an international audience
- Presented to defence personnel including David Neo and Major-General (MG) Lee Yi-Jin at SAF Day 2025
- GovWare networking directly led to SMU research internship offer
03 // MEDIA

Human Resources Online
Temasek Polytechnic Students Step In to Strengthen MSME Cybersecurity

Temasek Polytechnic
TP Launches Cybersecurity Clinic, Empowering Students to Strengthen MSME Digital Resilience
TP IIT (Facebook)
First Batch of DIS Cyber Specialists Under Work-Learn Scheme

TP IIT (Facebook)
Cybersecurity Clinic Video Feature
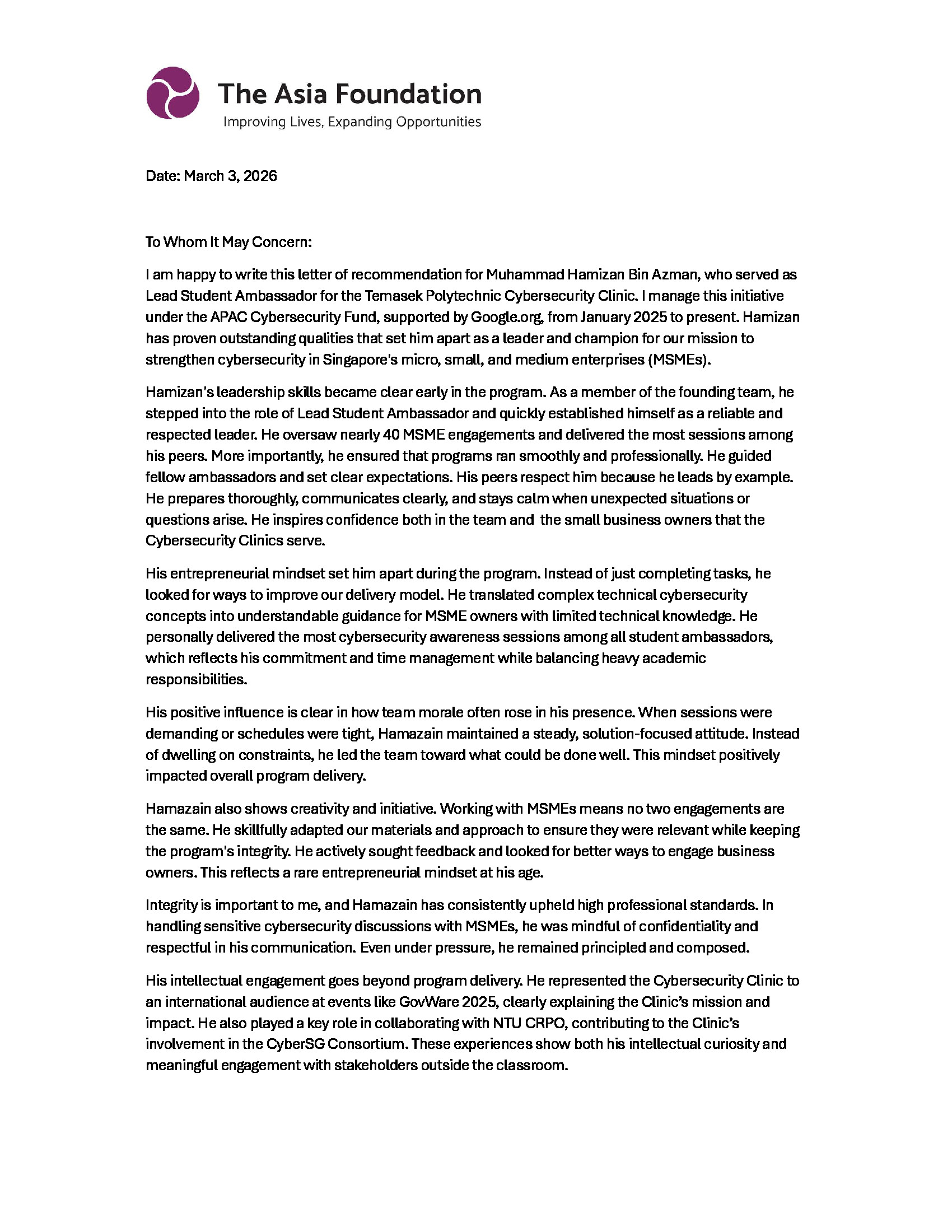
04 // TESTIMONIAL
“I recommend him without reservation and am confident he will continue to excel in any academic or professional setting he chooses to pursue. He is a capable leader, a reliable team member, and a young professional of integrity and promise.”
05 // CERTIFICATIONS
CompTIA Security+ SY0-701
CompTIA
Industry standard cybersecurity certification. Funded by AMP Singapore.
HTB Certified Penetration Testing Specialist (CPTS)
Hack The Box
Advanced penetration testing certification. 7/28 modules completed. Exam voucher funded by AMP.
06 // PROJECTS
LLM Supply Chain App Deployments
Triaged 102 open source LLM and AI apps and deployed 79 of them as reproducible Docker images, with 83 pinned images now on Docker Hub under hoomzoom. Every deployed app has its own usage and reasoning docs, and the 23 that couldn't deploy each have a written failure analysis. Dependency pins sit in a V2 log so anyone in the lab can audit every version decision.
102
Apps Triaged
79
Deployed
83
Docker Images
TrustChain PenTest Engine
Engineering features into the lab's automated application pentest platform alongside a SMU PhD researcher. It runs as 26 Docker services behind a single entry port, with automated exploit generation, CVE search, DOCX report generation, and live progress streaming over SSE. The platform also exposes per tool progress at stage 1 and a partial automation mode with rerun support. Source is private but I can walk through it on request.
26
Microservices
8
Tasks Delivered
Vulnerability PoC Reproduction Framework
Reproduced 231 vulnerability PoCs as Dockerised shooting ranges. Each PoC includes a vulnerable server, attack script, Dockerfile, README, and reproduction notes. Identified duplicates and corrected inaccurate JSON fields across the dataset. Public dataset under hamizan-azman/llm-supply-chain-poc.
231
PoCs Reproduced
100%
Completion Rate
DeepVysion+ @ GovWare 2025 & SAF Day

Presented the DeepVysion+ multimodal deepfake detection platform (Best Major Project, 2024 cohort) at GovWare 2025 to an international cybersecurity audience. Also presented to defence personnel including David Neo and Major-General (MG) Lee Yi-Jin, along with other SAF and DIS staff.
#1
Best Major Project
GovWare
Presented At
Vulnerability Research

Active disclosure work across open source authentication, mail, and protocol implementations. Two CVEs rewarded so far, with further disclosures in progress alongside a collaborator.
- RewardedCVE-2026-27855 (Dovecot, CVSS 6.8 Medium). auth_cache_remove() uses the wrong username field, allowing OTP replay when passdb rewrites the username during improper authentication.
- RewardedSecond vulnerability reported via HackerOne with accepted CVSS 6.9 and bounty paid. CVE identifier still being assigned.
- In progressAdditional open source disclosures in progress with a collaborator. Details withheld until reports are public.
2
CVEs Rewarded
+
More In Pipeline
07 // IMPACT
2
CVEs Rewarded
Dovecot CVSS 6.8 plus HackerOne CVSS 6.9. More disclosures in progress
231
Vulnerability PoCs Reproduced
100% completion rate across full dataset
79
LLM Apps Containerised
Reproducible Docker images pushed to Docker Hub
38
MSMEs Supported
Businesses secured through Cybersecurity Clinic
40
Ambassadors Trained
Recruited and mentored as Lead Student Ambassador
12
On Site Programmes
Most of any ambassador, conducted physically
2
Internship Offers On Site
Companies offered positions during clinic engagements
08 // CONTACT
Let's connect.
I'm open to research collaborations, mentorship opportunities, and conversations about AI/LLM security. Currently based in Singapore.
20 · pre-undergrad · focus on AI/LLM security
Built by Hamizan Azman · hamizanazman.com